Vpns Proxies And Zscaler Whats The Difference And Do You Need Them: A Complete Guide For VPNs, Proxies, And Zscaler
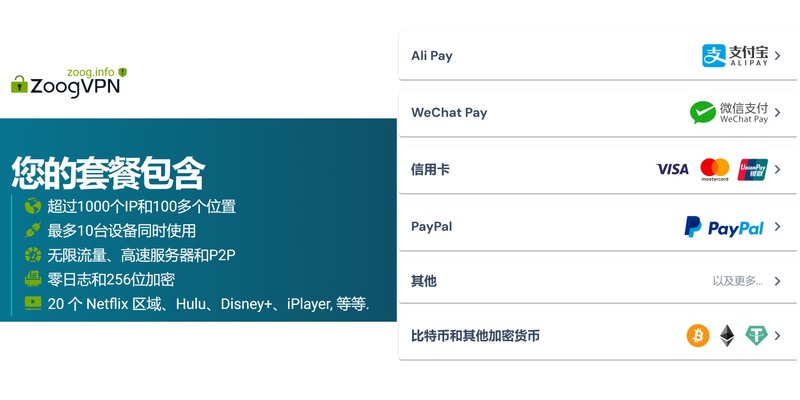
Vpns proxies and zscaler whats the difference and do you need them? Here’s the quick answer: they’re all tools to help you stay private, access restricted content, and protect data, but they serve different purposes and fit different scenarios. In short, you usually don’t need all three at once, but understanding how each works helps you pick the right tool for your situation. If you want a practical starting point, check out the NordVPN deal through this link: NordVPN — it’s a simple way to kick things off and stay secure while browsing.
Vpns proxies and zscaler whats the difference and do you need them? A quick fact: VPNs, proxies, and Zscaler are all designed to route your traffic through third-party networks to improve privacy, bypass geofencing, or enforce security policies, but they do this in different ways and for different use cases. This guide breaks down what each option does, how they’re used in real life, and when you should consider them.
- Quick overview:
- VPNs encrypt your traffic and route it through a remote server, protecting your data on public networks and masking your IP.
- Proxies relay your requests through a server, but most don’t encrypt traffic, making them faster for certain tasks but less private.
- Zscaler is a cloud security platform focused on policy enforcement, threat protection, and secure access for businesses, often used to protect employees and manage access to apps.
- Who should use each:
- Everyday privacy and secure browsing: VPNs are usually the best balance of privacy, security, and ease of use.
- Light masking or specific task routing like scraping or geo-testing: Proxies can be handy, but watch for privacy gaps.
- Enterprise security and secure access: Zscaler shines in organizations that need centralized policy control, threat protection, and seamless access to internal apps.
- Quick-start resources:
- VPN setup guide, VPN comparison, Proxy basics, Zscaler overview, and enterprise security best practices.
- Useful URLs and Resources text only, not clickable:
- NordVPN – nordvpn.com
- Wikipedia – en.wikipedia.org
- Zscaler – zscaler.com
- Cloudflare – cloudflare.com
- Apple Website – apple.com
- Google Privacy – google.com/privacy
Section: What is a VPN and how it works
- Definition and core functions
- A Virtual Private Network VPN creates an encrypted tunnel between your device and a VPN server, masking your IP address and shielding your traffic from being read by others on the same network.
- Encryption standards to look for: AES-256, OpenVPN, WireGuard. These are widely regarded as secure and efficient.
- Typical use cases
- Public Wi-Fi protection, bypassing geo-restrictions for streaming, and keeping online activity private from ISPs or network admins.
- Pros and cons
- Pros: Strong privacy, encryption, easy to use, broad server networks.
- Cons: Potential slowdown due to encryption overhead, some services block known VPN IPs, can be overkill for casual browsing.
Section: What is a Proxy and how it differs from a VPN
- Types of proxies
- HTTPS proxies for web traffic, SOCKS proxies for a broader range of traffic, and transparent proxies that don’t require config changes.
- How proxies work
- Proxies relay your requests through a remote server. Most proxies don’t encrypt traffic by default, which means your data could be read if the connection isn’t HTTPS.
- When proxies are useful
- Bypassing simple geo-restrictions for browsing, testing regional content, or doing quick web scraping where encryption isn’t needed.
- Pros and cons
- Pros: Usually faster, flexible for specific tasks, often cheaper or free options.
- Cons: No encryption by default, IPs can be blocked, logging policies vary, less privacy protection.
Section: What is Zscaler and how it fits in
- What Zscaler does
- Zscaler is a cloud security platform that provides secure access to the internet and internal apps, threat protection, data loss prevention, and policy enforcement. It’s designed for teams and enterprises.
- Core components
- Zscaler Internet Access ZIA: Secure internet access, inline security, and policy enforcement.
- Zscaler Private Access ZPA: Secure access to internal apps without a traditional VPN.
- Why enterprises choose Zscaler
- Centralized management, scalable security for remote workers, reduced risk from compromised devices, and granular policy control.
- Pros and cons
- Pros: Strong security posture, centralized control, easy deployment for large teams.
- Cons: More complex setup, typically requires IT involvement, not usually aimed at individual consumers.
Section: VPNs vs proxies vs Zscaler: A side-by-side comparison
- Encryption and privacy
- VPN: Encrypts all traffic between you and the VPN server. Proxies typically do not encrypt traffic unless paired with HTTPS and a secure tunnel.
- Zscaler: Encrypts and inspects traffic as part of security policy, but visibility and protection are driven by enterprise configurations.
- Scope of protection
- VPN: Covers all app traffic from your device while connected.
- Proxy: Typically applies to a subset of apps or browser traffic, depending on configuration.
- Zscaler: Applies at the organization level, covering users, devices, and traffic to protect web and app access.
- Complexity and management
- VPN: Moderate setup; consumer-grade VPNs are user-friendly but enterprise-grade VPNs can be complex.
- Proxy: Simple for browsers or specific apps; may require manual setup for non-browser traffic.
- Zscaler: Enterprise-grade, centralized management with policy enforcement and telemetry.
- Performance impact
- VPN: Potential slowdowns due to encryption, server distance, and carrier routing.
- Proxy: Often faster for simple tasks but can be unreliable if proxies are overloaded or poorly configured.
- Zscaler: Cloud-based, optimized for performance, but can introduce latency in initial inspections.
- Use-case fit
- VPN: General privacy, secure browsing on public networks, bypassing geo restrictions.
- Proxy: Lightweight masking, web scraping, or testing geolocated content.
- Zscaler: Organizations needing strong security, centralized policy, and secure access to internal apps.
Section: Real-world scenarios and recommendations
- Scenario 1: You want to protect privacy on public Wi-Fi and access geo-restricted services
- Recommendation: Use a reputable VPN with strong encryption and a wide server network. Look for no-logs policy, DNS leak protection, and kill switch.
- Quick setup steps:
- Choose a VPN provider with strong reviews and a clear privacy policy.
- Install the VPN app on your device.
- Connect to a nearby server, then test for DNS leaks and IP address.
- Scenario 2: You need to perform web scraping or test content from multiple locations
- Recommendation: Proxies can help, but ensure you comply with terms of service and use rotating proxies or a proxy service with good privacy policies. For sensitive tasks, consider VPN plus proxy combo cautiously.
- Quick setup steps:
- Decide on the proxy type SOCKS5 for broad use, HTTPS for web traffic.
- Configure your browser or scraping tool to route traffic through the proxy.
- Monitor for IP blocks and adjust rotation frequency.
- Scenario 3: Your company wants to secure remote employees and protect internal apps
- Recommendation: Zscaler ZIA and ZPA is a strong enterprise-grade choice, offering centralized policy, threat protection, and seamless access to apps.
- Quick setup steps:
- Work with IT to deploy Zscaler client or integration with existing devices.
- Define security policies, acceptable use, and app access rules.
- Train users on how to connect and what to expect during security checks.
Section: Security, privacy, and best practices
- Privacy considerations
- Not all VPNs are equally privacy-focused; read their privacy policy and understand logging practices.
- Proxies may log traffic, which could reveal sensitive information if not properly managed.
- Security hygiene
- Keep software up to date, enable multi-factor authentication where available, and use trusted providers with transparent policies.
- Data protection tips
- Avoid logging into sensitive accounts over untrusted networks, verify DNS and VPN kill switch functionality, and test for IP leaks regularly.
- Performance tips
- Choose servers near your location for the best speed, use WireGuard or modern protocols when available, and enable features like split tunneling if you only need protection for certain apps.
Section: How to choose the right tool for you
- Quick questions to guide your choice
- Do you primarily need privacy on public networks? Go with a VPN.
- Do you need targeted access for specific apps or web tasks? A proxy might suffice, but evaluate privacy and encryption needs.
- Are you in an organization needing centralized policy protection and secure internal access? Zscaler is the solid enterprise choice.
- Budget and support
- Consumer VPNs are typically affordable with monthly plans; proxies can be cheap or free but with caveats; enterprise solutions like Zscaler involve larger investments and IT support.
- Compatibility
- Ensure your device, operating system, and required apps support the chosen solution.
Section: Common myths and misconceptions
- Myth: A VPN makes you completely anonymous online
- Reality: A VPN hides your IP and encrypts traffic, but it doesn’t make you invisible. Log policies, behavior, and endpoint security still matter.
- Myth: Proxies provide the same privacy as VPNs
- Reality: Proxies may hide your IP, but without encryption, your data can be exposed, especially on public networks.
- Myth: Zscaler is only for big companies
- Reality: While Zscaler is enterprise-focused, some smaller teams and managed service providers use ZIA/ZPA for scalable security.
Section: Data and statistics you can trust
- Global VPN market size and growth
- The VPN market has seen steady growth with increasing demand for privacy and secure remote work. Analysts predict continued expansion into 2025 and beyond.
- Proxy usage trends
- Proxies are popular for testing and data collection, but consumer use is less common than VPNs for personal privacy.
- Enterprise security adoption
- More organizations are migrating to cloud-based security platforms and zero-trust architectures, with Zscaler and similar solutions playing major roles.
Section: Setup checklists and quick-start guides
- VPN quick-start checklist
- Pick a reputable VPN with strong privacy policy and security features.
- Install on all devices you use regularly.
- Enable kill switch, DNS leak protection, and auto-connect on startup.
- Test IP address, location, and speed after connection.
- Proxy quick-start checklist
- Choose the right proxy type and provider with a clear privacy policy.
- Configure your browser or app to use the proxy.
- Verify traffic routing and monitor for IP consistency.
- Zscaler quick-start checklist enterprise
- Coordinate with IT for deployment on devices.
- Define security policies, access rules, and user training.
- Run pilot tests and monitor security telemetry to refine rules.
Section: Ethical and legal considerations
- Respect terms of service
- Many services prohibit the use of anonymization tools to bypass geo-restrictions or content paywalls. Be mindful of terms and conditions.
- Compliance and data protection
- Ensure your use aligns with local laws and company policies, especially when handling sensitive data.
Section: FAQ Section
Frequently Asked Questions
Do I need a VPN if I already use Zscaler?
A: If you’re an individual user and your goal is private browsing on public networks, a VPN is typically a better fit. Zscaler is an enterprise security platform designed for organizations to protect users and apps. Some workplaces may configure VPN-like secure access alongside Zscaler, but for personal use, a VPN is usually sufficient.
Can proxies replace a VPN for privacy?
A: Proxies can hide your IP, but they usually don’t encrypt traffic, which means your data can be exposed on untrusted networks. For privacy and security, a reputable VPN is generally a better choice.
Is Zscaler expensive for small businesses?
A: Zscaler pricing varies by tier and deployment scale. While it’s most common in larger organizations, smaller teams can adopt it if they need centralized policy and cloud security. It’s worth contacting a sales rep for a tailored quote.
How is VPN speed affected?
A: VPN speed depends on server distance, encryption overhead, and server load. Choosing a nearby server and a modern protocol like WireGuard can help minimize slowdowns.
Are there free VPNs worth using?
A: Free VPNs often come with limitations, data caps, and questionable privacy practices. For serious privacy and security, a paid, reputable VPN with a transparent policy is recommended. Softether vpn download 최신 버전 설치부터 활용까지 완벽 가이드
Can I use VPN and proxy together?
A: It’s possible to use both, but it can complicate routing and reduce performance. If you need specific tasks routed through a proxy, consider split tunneling with your VPN to minimize overhead.
How does ZPA differ from traditional VPNs?
A: ZPA provides zero-trust access to internal apps without creating a full network tunnel. It’s designed for secure, remote access with centralized policy, rather than routing all traffic through a remote VPN server.
What features should I look for in a VPN?
A: Strong encryption AES-256, a no-logs policy, DNS leak protection, a kill switch, a wide server network, and user-friendly apps. Also check privacy reviews and independent audits when possible.
Can VPNs bypass government censorship?
A: VPNs can help bypass certain regional restrictions and censorship, but this is not guaranteed. Some regions actively block VPN traffic, so results vary and users should stay informed about local laws.
How do I verify that my VPN is protecting me?
A: Run an IP and DNS leak test, verify that your real IP isn’t exposed, and check that your traffic appears to be originating from the VPN server. Use reputable tools and services for testing. Browsec vpn extension for microsoft edge a comprehensive guide to enhanced browsing
End of content
Sources:
银河VPN:全面解读、选购指南与实用技巧
バッファロー製ルーターでvpn接続を設定する方法 応用ガイド
免费翻墙vpn:全面指南与最新趋势,选择、使用与安全要点
Att vpn not working heres exactly how to fix it Как использовать vpn для браузера microsoft edge пол: практическое руководство по защите приватности и ускорению серфинга
Clash 梯子搭建:手把手教你从零开始配置,告别网络限制