Is vpn safe for ifr heres what you need to know: a practical guide to VPN safety, risks, and best practices
Is vpn safe for ifr heres what you need to know? Quick fact: VPNs can improve privacy and security, but they’re not a silver bullet and not all VPNs are created equal. In this guide, you’ll get a clear, actionable rundown on how VPNs work, safety considerations, and how to choose a VPN that actually protects you. Below you’ll find a mix of practical tips, real-world examples, data, and a step-by-step checklist you can use today.
- Quick overview: VPNs encrypt your traffic, mask your IP, and help you bypass geo-restrictions. But some providers log data, leak DNS, or sell your info. The safest approach is to pick a reputable VPN with a clear no-logs policy, strong encryption, and independent audits.
- What you’ll learn in this post:
- How VPNs work at a high level
- Common safety concerns and how to mitigate them
- How to pick a VPN that fits your needs privacy, streaming, gaming, work
- Real-world stats on VPN usage and data protection
- A practical setup guide with step-by-step actions
- A cheat sheet and a list of trustworthy resources
Useful resources text only, not clickable: Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, VPN Privacy Statistics - vpnstats.org, Data Breach Reports - breachlevelindex.com, ENISA Threat Landscape - enisa.europa.eu/threat-landscape
Table of contents
- How VPNs work: the basics you need
- Safety concerns and how to address them
- VPN for streaming, work, and casual browsing: which one to pick
- Practical setup: steps you can take now
- Common myths about VPNs debunked
- Real-world data and privacy considerations
- Choose with confidence: a checklist
- Resources and further reading
How VPNs work: the basics you need
- Encryption and tunnels: A VPN creates an encrypted tunnel between your device and a VPN server. Your internet traffic is wrapped in a cipher, so outsiders can’t easily read it.
- IP masking: Your real IP is replaced with the VPN server’s IP. This makes you appear to be somewhere else.
- Privacy vs. security: VPNs improve privacy from local network observers like public Wi-Fi and sometimes protect you from DNS leaks, but they don’t make you invisible online or protect you from all tracking.
- Logs, policy, and audits: Not all VPNs behave the same. Some log metadata, some don’t log at all, and independent audits can verify claims. Look for a transparent privacy policy and third-party audits.
Safety concerns and how to address them
- Logging and data retention: Some VPNs log connection timestamps, server locations, or bandwidth. Mitigation: choose a provider with a clear no-logs policy and independent audits. Check court case history or legal disclosures in the provider’s country.
- DNS leaks: Even with a VPN, DNS queries can leak to your ISP, revealing sites you visit. Mitigation: enable DNS leak protection in the app, or use a VPN with built-in DNS leak resistance.
- IP leaks: Rare but possible if the VPN drops or misconfigures. Mitigation: enable the kill switch feature so traffic stops if the VPN disconnects.
- Malware and fake apps: Some VPN apps are malicious or bundled with adware. Mitigation: download from official sources, check app permissions, and read independent reviews.
- Trust and governance: Jurisdiction matters. Some countries compel data retention or data sharing. Mitigation: use a provider with strong privacy laws or a country with favorable privacy safeguards, and consider multi-hop or no-logs configurations.
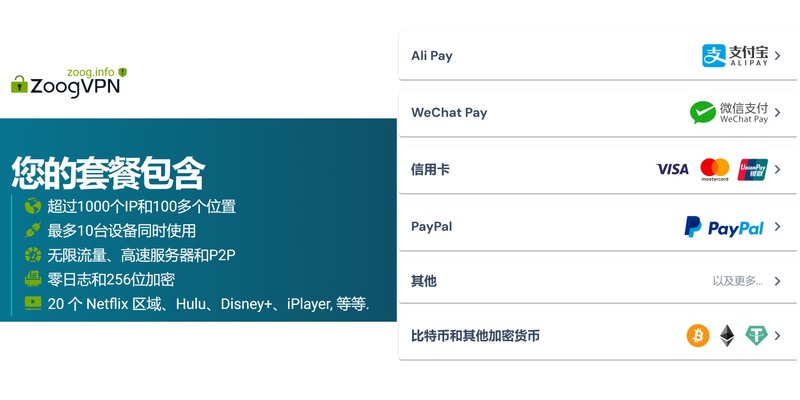
- Payment anonymity: Some services require credit cards, which can be linked to you. Mitigation: use prepaid methods or cryptocurrencies where legal and appropriate, while staying aware of tracing risks.
VPN for streaming, work, and casual browsing: which one to pick
- Streaming and geo-b bypass: If you want to access region-locked content, look for servers in multiple countries and fast speeds. Be mindful of streaming platform blocks and rotating IPs.
- Work and secure remote access: For remote workers, a VPN with business-grade security, split tunneling controls, and robust authentication 2FA is key. Ensure a provider supports enterprise-grade protocols and compatibility with your work infrastructure.
- Casual browsing and privacy: Any reputable VPN with strong encryption, a no-logs policy, and user-friendly apps will do. Prioritize ease of use and reliability.
Practical setup: steps you can take now
- Step 1: Define your goals
- Are you protecting public Wi‑Fi, bypassing geo-restrictions, or securing work traffic?
- Step 2: Choose the right VPN
- Look for: no-logs policy, independent audits, strong encryption AES-256, secure protocols OpenVPN, WireGuard, kill switch, DNS leak protection, and transparent governance.
- Step 3: Check jurisdiction and audits
- Favor providers in privacy-friendly jurisdictions and with recent third-party audits.
- Step 4: Install and configure
- Use official apps, enable kill switch, enable IKEv2/OpenVPN/WireGuard with best available settings, enable DNS leak protection.
- Step 5: Test for leaks
- Use online tools to check IP address, DNS, and WebRTC leaks when connected to the VPN.
- Step 6: Use strong authentication
- Enable 2FA, use unique passwords, and consider device-level passcodes or biometric protection.
- Step 7: Manage devices and profiles
- For work, segregate personal and business devices, and apply consistent settings across devices.
- Step 8: Monitor and renew
- Regularly review permissions, logs if any, and keep apps up to date. Plan for audits or policy reviews if needed.
- Step 9: Backups and recovery
- Keep recovery options for your VPN account, especially if it’s a work-provided service.
Data and privacy considerations
- Global VPN market: The VPN market is growing rapidly, with widespread use for privacy, security, and access. Analysts estimate tens of millions of daily VPN users, with a multi-billion-dollar market.
- Privacy impact: Even with a VPN, advertisers and websites may still track you via fingerprinting, cookies, and social profiles. A VPN complements other privacy measures but isn’t a complete solution.
- Speed and performance: VPN encryption can introduce latency and slower speeds. The impact varies by provider, server distance, and network conditions. Many top providers now optimize for low-latency performance with WireGuard and other modern protocols.
- Legal considerations: In some jurisdictions, using a VPN is restricted or regulated. Always follow local laws and terms of service for the platforms you use.
Myths about VPNs debunked
- Myth: VPNs hide illegal activity. Reality: They can hide certain patterns from local network observers, but they don’t grant immunity from law enforcement. Usage still must comply with laws.
- Myth: Any VPN is safe. Reality: Safety depends on the provider’s policies, encryption standards, and practices. Free VPNs often come with trade-offs.
- Myth: VPNs are only for avoiding censorship. Reality: VPNs are widely used for security on public Wi‑Fi, privacy, and accessing content from other regions.
Real-world data and privacy considerations
- HTTPS adoption: Even with a VPN, using HTTPS websites is crucial for end-to-end encryption. VPNs protect data in transit between you and the VPN server, but HTTPS protects data in transit between the server and the destination.
- Malware risk: Some VPN apps have been found to include adware or tracking libraries. Stick to reputable providers and verify app integrity.
- Data breach risk: If a provider experiences a data breach or is compelled to share data, your information could be exposed. Favor providers with audited no-logs policies and robust data protection measures.
Choose with confidence: a practical checklist
- Privacy policy: Read the policy carefully. Is there a no-logs statement you can verify?
- Independent audit: Has the service undergone an independent security audit? Are the findings publicly available?
- Encryption and protocols: Does the provider offer AES-256 encryption and modern protocols like WireGuard and OpenVPN?
- Kill switch and leak protection: Are DNS and IP leak protections built-in and enabled by default?
- Jurisdiction and legal framework: Where is the company headquartered, and what are the data retention laws?
- Server network: How many servers and which locations? Are there specialty servers P2P, streaming, gaming?
- Speed and reliability: Can you test the service with a trial or 30-day money-back guarantee? Are there reports of frequent disconnects?
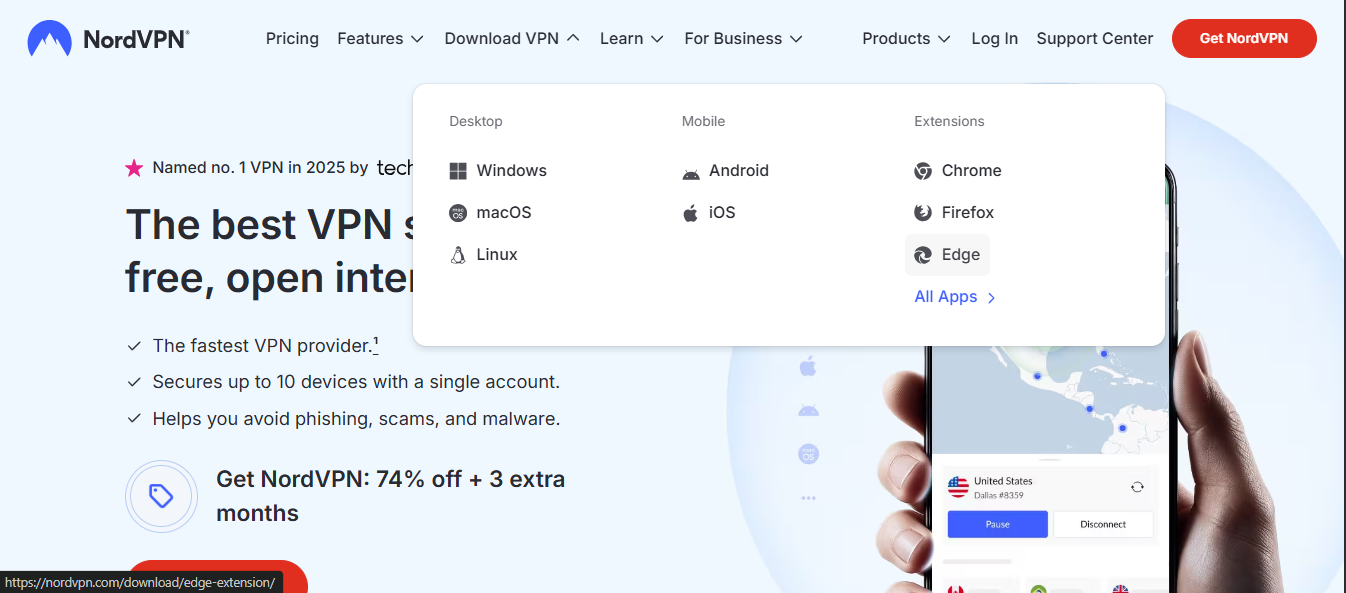
- Compatibility: Does it work on all your devices Windows, macOS, iOS, Android, routers?
- Customer support: Is there 24/7 support and clear guidance for setup and troubleshooting?
- Price and value: Compare plans, features, and limits. Are there hidden costs or data caps?
FAQ Section
Frequently Asked Questions
How does a VPN protect my privacy on public Wi‑Fi?
A VPN encrypts your data, making it much harder for others on the same network to see what you’re doing. It also hides your IP, which helps you avoid local profiling based on your location.
Can a VPN be trusted for sensitive work data?
Yes, if you choose a provider with a solid no-logs policy, strong encryption, and enterprise-grade features like double-factor authentication and split tunneling controls. For highly sensitive data, consider additional security measures like zero-trust access and company-managed VPNs.
Do VPNs block tracking and ads?
Many VPNs reduce some tracking by masking your IP, but they don’t inherently block all ads or tracking. Use a privacy-focused browser, tracker blockers, and consider pairing with a reputable DNS service or privacy extension.
What is a kill switch, and why do I need it?
A kill switch stops all internet traffic if the VPN disconnects unexpectedly, preventing your real IP from being exposed. It’s a critical safety feature.
Can VPNs leak my real IP or DNS?
DNS leaks and IP leaks are possible but avoidable with proper configuration. Always enable DNS leak protection and test for leaks after setup. Nordvpn mit ikev2 auf ios 18 verbinden deine schritt fur schritt anleitung
Do I need a VPN if I use HTTPS everywhere?
HTTPS protects the content of your communications, but a VPN adds protection over local networks, hides your IP, and can bypass some geo-restrictions. They complement each other.
Are free VPNs safe?
Free VPNs often come with restrictions, fewer servers, slower speeds, and questionable privacy policies. Paid, reputable VPNs are usually a better choice for real privacy and security.
How many devices can I protect with one VPN subscription?
Most premium VPN plans cover multiple devices usually 5–7. If you have a larger setup, check the provider’s limits or consider a business plan.
Can VPNs be used on routers?
Yes. Installing a VPN on your router can protect all devices on your network, but it requires some technical setup and compatible router hardware.
How do I verify a VPN’s no-logs claim?
Look for independent security audits, legal documents, and transparency reports. Third-party audits provide the strongest validation of no-logs promises. Scaricare e usare una vpn su microsoft edge guida completa 2026: Guida completa, consigli pratici, vantaggi e FAQ
Why this matters for you
- Real-world impact: VPNs are a practical tool for privacy, security, and access. If used correctly, they reduce exposure on public networks and help you control who sees your online behavior.
- Practical mindset: Treat a VPN as part of a layered privacy strategy rather than a magic shield. Combine it with strong passwords, device security, and mindful online habits.
Affiliate note If you’re exploring a VPN for privacy and security, consider giving NordVPN a try. It’s one of the more consistently reviewed services in terms of privacy policy transparency and independent audits. If you’re curious, you can check it out via this link: NordVPN and see if it fits your needs. For readers, the text above mentions the provider’s reliability in general terms; always review current terms, pricing, and audits directly on the official site to confirm.
Final thoughts
- Is vpn safe for ifr heres what you need to know? Yes, with the right provider and correct setup, a VPN can enhance your privacy and security. It’s not a universal fix, and you should pair it with good device hygiene, secure networks, and mindful online behavior.
- Quick-start action plan:
- Choose a reputable VPN with independent audits and a no-logs policy.
- Install on your most-used devices and enable kill switch and DNS leak protection.
- Test for leaks and verify no logs with the provider’s resources.
- Use it consistently on public networks and when privacy matters most.
Notes for creators
- If you’re making a YouTube video based on this guide, you can structure it as a step-by-step tutorial, include on-screen checks kill switch, DNS leak test, real-world examples public Wi‑Fi scenario, and a quick “how to pick a VPN” decision tree. Include time-stamped sections for easy navigation, and reference the privacy audit standings and policy links in the description for viewers seeking deeper verification.
Sources:
Vpn使用方法:完整跨平台设置、隐私保护、速度优化与常见问题解答 초보자도 쉽게 따라 하는 미꾸라지 vpn 사용법 완벽 가이 - VPN 활용법, 속도 최적화, 보안 팁까지 한눈에
Azure vpn from china 在中国使用 Azure VPN 的完整指南
Hkmc rnd vpn hyundai net 현대자동차 rd 보안의 핵심: 현대의 VPN 전략과 보안 실전 가이드
Getting your money back a no nonsense guide to proton vpn refunds
Vpn违法:全面解读、使用与合规风险及替代方案