Finding Secure VPNs on GitHub: Your Guide to Open Source Privacy and Safe Open-Source Networking
Finding secure vpns on github your guide to open source privacy. A quick fact: open source VPN projects can be a goldmine for transparency, but they also carry risk if code isn’t audited. This guide breaks down how to find trustworthy VPNs on GitHub, what to look for, and how to verify safety before you trust an open-source project with your data.
- Quick-start overview
- Check for active maintenance and recent commits
- Review the code for obvious security flaws
- Look for independent audits or community trust signals
- Consider using a well-known project with a strong privacy track record
- Why open source VPNs matter
- Transparency means you can inspect what the client does
- Community scrutiny can reveal hidden telemetry or leaks
- However, “open source” doesn’t automatically equal “secure”—you still need due diligence
Introduction condensed guide Finding secure vpns on github your guide to open source privacy is all about balancing transparency with practical safety. This video guide helps you quickly assess which open-source VPN projects on GitHub are worth your time, what to look for during a review, and how to minimize risk when you’re exploring code written by strangers. Below is a compact roadmap to help you decide whether a project is reputable enough to try, plus concrete steps to verify security, privacy, and reliability.
What you’ll learn Le vpn piu veloci del 2026 le abbiamo davvero provate: guida completa, compare e consigli pratici
- How to identify actively maintained projects
- The key indicators of trustworthy VPN software on GitHub
- Practical steps to audit open-source VPNs before use
- Common pitfalls and red flags in open-source VPNs
- How to test VPNs safely in real-world scenarios
Useful resources text only, not clickable
- Open Source Initiative - opensource.org
- GitHub Security Best Practices - github.com
- Common Vulnerabilities and Exposures CVE - cve.mitre.org
- OpenSSL Project - openssl.org
- Tor Project - www.torproject.org
- Mozilla Observability - observability.mozilla.org
- Linux Privacy and Security Guides - linuxsecurity.expert
Section: Why you should consider open-source VPNs
- Open-source advantages
- Transparency: you can review the code yourself or rely on audits
- Community vetting: issues, pull requests, and discussions reveal security concerns
- Reproducibility: you can build from source and verify the binary
- Open-source caveats
- Not every project is actively maintained
- Some projects might be forked without proper governance
- Build systems and dependencies can introduce risk if not managed
Section: How to find trustworthy VPNs on GitHub
- Step-by-step approach
- Start with reputation and maintenance
- Check stars aren’t enough: look for recent commits, active issues, and response time
- Review contributor activity: many maintainers vs. a single author can indicate robustness
- Audit the code path
- Look for client and server components, and how data flows
- Identify where logs are stored and what telemetry is sent
- Check for hard-coded secrets or insecure defaults
- Privacy policy and data handling
- See if the project has a privacy policy or design docs
- Look for statements about no-logging, data minimization, and onion routing if applicable
- Build and test process
- Confirm build instructions are clear and reproducible
- Check for CI tests, unit tests, and integration tests
- Validate forked projects don’t remove safety features
- Independent audits or third-party reviews
- Search for security reports, CVEs, or auditor notes
- Community feedback can indicate trustworthiness
- Community and governance
- Look for a code of conduct, governance model, and how issues are escalated
- Active issue discussion with transparent decisions is a good sign
- Start with reputation and maintenance
- Practical heuristics
- Prefer projects with a clear security model e.g., no-logs policy, data minimization
- Avoid projects that require you to disable security features or install unreviewed third-party modules
- Be wary of projects with suspiciously rapid release cycles and vague changelogs
Section: Key security indicators to verify
- Data handling and privacy
- What data is collected by the client DNS requests, IP exposure, telemetry?
- Is there end-to-end encryption, and what ciphers are used?
- Networking and DNS
- Are DNS leaks possible? Does the project implement DNS leak protection?
- Is there split tunneling, and if so, how is it configured?
- Authentication and keys
- How are credentials managed? Are there hard-coded keys or secrets in the repo?
- Are there secure key exchange mechanisms and proper certificate validation?
- Code quality and security practices
- Are there static analysis, fuzz testing, or regression tests?
- Do maintainers follow secure coding guidelines?
- Dependency security
- Are libraries up to date? How often are dependencies scanned for vulnerabilities?
- Are there submodules or nested dependencies that aren’t audited?
Section: Formats to help you digest quickly Is Mullvad VPN Good for China A Deep Dive into Bypassing the Great Firewall
Quick comparison table example
- Project | Last active | Maintainers | No-logs policy | Audit status
- VPN-OpenSource-Project A | 2 weeks ago | 4 maintainers | Claimed yes | Third-party audit: yes
- VPN-OpenSource-Project B | 6 months ago | 2 maintainers | Unclear | No audit
Checklist you can copy
- Active maintenance in the last 90 days: yes/no
- Clear privacy policy: yes/no
- End-to-end encryption implemented: yes/no
- DNS leak protection present: yes/no
- Independent security audit: yes/no
- Transparent issue history: yes/no
- Clean dependency management: yes/no
Section: How to verify a GitHub VPN project on your own
- Local build and verify
- Clone the repo and follow the build steps exactly
- Build from source and compare the produced binary hash with a trusted source
- Run unit tests and smoke tests in a controlled environment
- Safe testing practices
- Use a disposable VM or container when testing for the first time
- Don’t connect real accounts or sensitive data during initial tests
- Validate no traffic leaks through your network before trusting the tool
- Community validation
- Check issue discussions about security, leaks, or crashes
- Look for conversations about bug fixes and response times
- See if independent researchers or security groups have weighed in
Section: Performance and usability considerations
- Speed and latency
- VPN performance can vary by server location and protocol
- Compare the same test setup across different GitHub projects
- User experience
- How easy is the client to install and configure?
- Is there good documentation, tutorials, and examples?
- Cross-platform support
- Windows, macOS, Linux, Android, iOS
- How consistent is the experience across platforms?
- Resource usage
- CPU and memory footprints during idle and active use
- Impact on battery life for mobile devices
Section: Common scams and red flags on GitHub Whats a vpn on tiktok and do you actually need one: A Complete Guide to VPNs for TikTok Users
- Red flags to watch for
- Projects with no code, only compiled binaries
- Abandoned projects with vague commit messages
- Pull requests repeatedly closed without explanation
- Excessive reliance on external quick-start scripts with elevated privileges
- Safe alternatives
- Favor projects with open governance, public security notes, and auditor reports
- Choose well-known maintainers and community leaders
Section: Real-world scenarios and case studies
- Scenario 1: You’re evaluating a new open-source client
- Steps you take: review commits, read the code paths, check for telemetry
- Verdict: decide if you’ll test in a sandbox before use
- Scenario 2: A project claims no-logs but has DNS logging in a separate module
- Action: verify data flow and check policy statements across modules
- Outcome: determine if the project truly minimizes data collection
- Scenario 3: A project with a maintained fork
- Evaluate governance: who manages the fork, how is it aligned with the original project’s privacy goals
- Decision: weigh risks of fork divergence
Section: How to contribute safely to open-source VPNs
- If you want to contribute
- Start with small bug fixes or documentation updates to build trust
- Propose improvements for security or privacy features
- Engage respectfully in issues and pull requests
- How to report vulnerabilities
- Use the project’s responsible disclosure process if available
- Contact the maintainers privately if the process isn’t public
- Do not publish sensitive findings without consent
Section: Tools and resources for ongoing verification
- Security testing tools
- Static analysis tools to scan for vulnerabilities
- Network traffic analyzers to inspect data flows
- Fuzzing tools to test how the client handles unexpected input
- Privacy-focused testing
- DNS leak testing tools and websites
- IP address leak checks and VPN protocol verification
- Community signals
- Public bug bounty programs
- Independent audits and third-party reviews
- Transparent roadmaps and issue tracking
Section: FAQ Frequently Asked Questions
How do I know a GitHub VPN project is trustworthy?
Trust comes from active maintenance, transparent security notes, and independent audits. Look for recent commits, clear data handling policies, and community validation. Surfshark vpn not working fix no internet connection fast 2026 guide
What is the most important thing to check first?
Maintenance status. If a project hasn’t had activity in months, it’s a red flag, especially for security-focused tools.
Can open-source VPNs leak my data even if they’re open source?
Yes, open source is not a guarantee of privacy. Review the data collection practices, telemetry, and code paths to ensure no sensitive data is logged or leaked.
How can I test for DNS leaks?
Run the VPN with the DNS leak test enabled and use online DNS leak test services to verify that DNS queries aren’t leaking outside the tunnel.
Should I trust a VPN that uses proprietary components?
Be cautious. Proprietary components can hide security flaws. Prioritize projects with transparent components and full code access.
How often should I update an open-source VPN client?
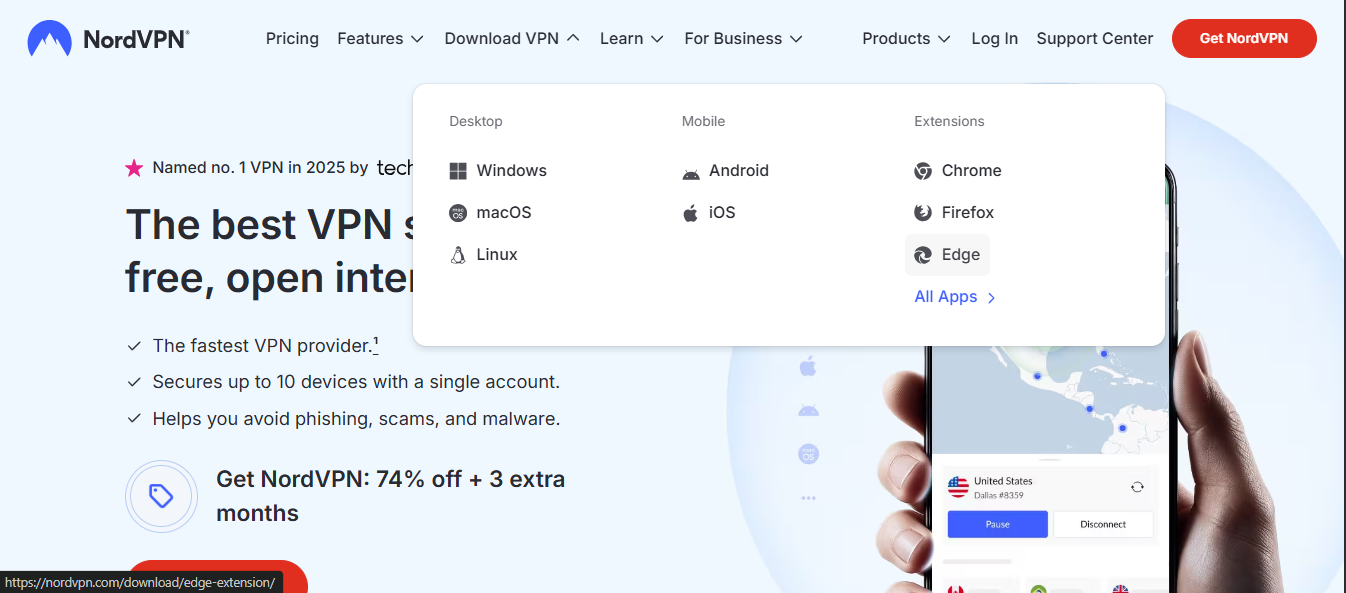
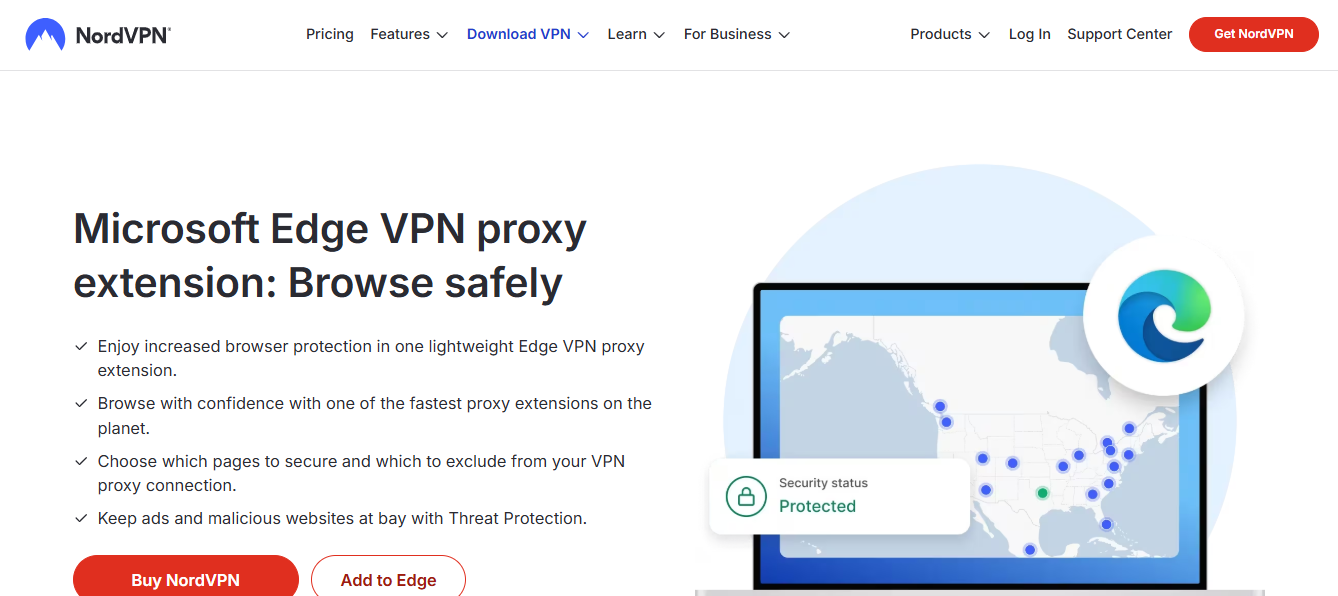
Keep up with the latest releases and security advisories. Apply updates promptly when patches address critical vulnerabilities. Nordvpn browser extension for microsoft edge a comprehensive guide for 2026
What’s the role of independent audits?
Audits provide a third-party assessment of security claims and identify potential vulnerabilities that maintainers might miss.
How can I assess a project’s privacy policy if one exists?
Read for data collection details, retention periods, and whether data is shared with third parties. Look for explicit no-logs statements where applicable.
Can I use GitHub to host my own VPN client securely?
Yes, but you still need to implement strong security practices, thoroughly review dependencies, and consider independent audits before distributing.
What should I do before using any open-source VPN in production?
Test in a controlled environment, verify TLS configurations, review code paths for data handling, and ensure there are known-good builds from trusted sources.
FAQ: Additional practical tips Surfshark vpn very slow heres how to fix it fast: Surfshark VPN Slow Fixes, Speed Tips, and Troubleshooting
- Always build from source when possible to verify binaries
- Prefer projects with clear governance and documented security practices
- Use a sandboxed environment to test new VPN clients before wide deployment
In closing Finding secure vpns on github your guide to open source privacy is about more than just finding a project with the word “vpn” in its name. It’s about applying a careful, methodical approach to verify security, privacy, and ongoing maintainability. By checking maintenance activity, auditing code paths, reading privacy policies, and validating through independent reviews and community feedback, you’ll be better equipped to pick open-source VPNs that respect your privacy and keep your data safer online.
NordVPN affiliate link integration example If you’re looking for a trusted option to complement your open-source testing, consider trying NordVPN for additional security coverage and peace of mind. You can explore this option here: NordVPN. This resource can provide a reliable companion as you test and compare open-source VPN solutions, ensuring you have a secure fallback as you explore GitHub projects for privacy-focused networking.
Sources:
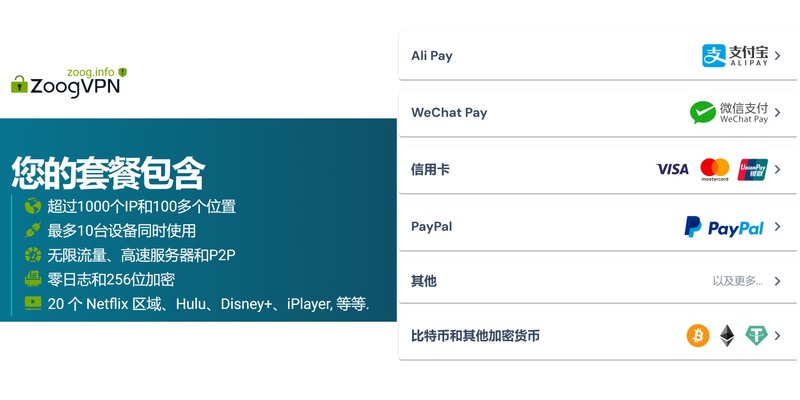
快喵vpn官网:全面解析、实用指南与最新数据,VPN选择全流程
The Ultimate Guide to the Best VPN for Vodafone Users in 2026: Fast, Secure, and Vodafone-Friendly
Le cout de mysterium vpn ce quil faut vraiment savoir Tiktok Not Working in China Even With a VPN Here’s The Real Reason: Why The Great Firewall Wins And How To Bypass Safely
Vpn永久长期稳定使用的完整指南:如何实现、评估与常见问题解答
Free vpn browser extension edge